Questions for you:
- When evaluating security systems, do you understand the difference between true randomness (physical unpredictability) and pseudorandomness (computational unpredictability), and when each is appropriate?
- Looking at password policies requiring “random” passwords, do you recognise that human-generated “random” passwords unconsciously introduce patterns (avoiding repeated digits, preferring specific numbers) that dramatically reduce effective security?
- When assessing cryptographic systems, do you verify that random number generation is properly implemented with adequate entropy sources, or assume all “random” generation is equivalent?
- In designing security protocols, do you understand that practical unpredictability (pseudorandomness) is often preferable to theoretical randomness due to speed, reproducibility, and verifiability requirements?
Organisational applications:
Cryptographic PRNGs for speed and security: Most digital security uses pseudorandom number generators, not true randomness. PRNGs work like mathematical recipes: feed them a random seed, and they produce millions of statistically random numbers through entirely deterministic processes. A good cryptographic PRNG generates millions of random-looking numbers per second on ordinary hardware, essential for real-time encryption, secure networking protocols, and generating session keys for millions of simultaneous users. Security comes from computational complexity – even knowing the exact algorithm, predicting the next number without a seed requires solving mathematical problems, which takes centuries on every computer on Earth. This practical unpredictability often beats theoretical randomness.
Seed security and entropy sources: The entire PRNG security depends on a truly random seed. If attackers guess or determine initial seed value, they can reproduce entire sequence – catastrophic security failure. This is why PRNGs in security applications are seeded with entropy from True Random Number Generators (TRNGs), which can be derived from mouse movements, keyboard timing, thermal noise, atmospheric interference, or quantum-mechanical processes. Never allow human-generated seeds (people unconsciously introduce patterns). Verify that security-critical systems use adequate entropy sources, regularly reseed PRNGs, and combine multiple entropy sources for defence-in-depth.
Human randomness failure and password security: When people try creating random passwords or PINs, they unconsciously introduce patterns – avoiding repeated digits, preferring specific numbers (often birthdays), following predictable substitution rules (replacing ‘E’ with ‘3’). These human biases dramatically reduce effective security, turning a lock with trillions of combinations into one with just thousands. Attackers exploit these patterns through dictionary attacks, prioritising common human patterns. Organisational password policies must require computer-generated random passwords, use password managers to eliminate human bias, and educate users that “memorable” passwords are predictably weak.
Reproducibility and debugging advantages: PRNGs offer a critical advantage over true randomness: reproducibility. Given the same seed, PRNG produces the same sequence every time. This enables debugging security systems (reproducing the exact conditions that triggered failures), testing cryptographic protocols (verifying that implementations match specifications), and creating verifiable audit trails (proving that cryptographic operations were performed correctly). True randomness lacks this property – you can never reproduce the exact sequence. For many security applications, deterministic unpredictability is more valuable than non-deterministic randomness.
Further reading
Pseudorandom number generation and cryptographic security
Cryptography Engineering by Niels Ferguson, Bruce Schneier, and Tadayoshi Kohno – practical cryptography guide including detailed coverage of PRNG design, implementation, and security properties showing why pseudorandomness suffices for most security applications.
The Code Book by Simon Singh – accessible history of cryptography explaining how random key generation became foundation of modern encryption and why computational unpredictability protects digital communications.
Applied Cryptography by Bruce Schneier – comprehensive cryptography reference including extensive discussion of random number generation, PRNG algorithms, and seed security requirements.
Entropy, true randomness, and computational complexity
Randomness by Deborah J. Bennett – examines nature of randomness including discussion of deterministic systems producing unpredictable outputs, showing philosophical and practical differences between true and pseudo randomness.
The Drunkard’s Walk by Leonard Mlodinow – whilst primarily about probability, discusses randomness generation and why computational unpredictability can be more useful than physical randomness for practical applications.
Secrets and Lies by Bruce Schneier – security expert’s examination of digital security showing critical importance of proper random number generation and common failures when entropy sources are inadequate.
Security failures and human randomness bias
Fatal System Error by Joseph Menn – cybercrime investigation including examples of security breaches exploiting predictable “random” number generation and weak entropy sources.
Security Engineering by Ross Anderson – comprehensive security engineering textbook including case studies of security failures from inadequate random number generation and human bias in password selection (available free online).
Click Here to Kill Everybody by Bruce Schneier – discusses modern security challenges including why human intuition fails at creating randomness and consequences of weak random number generation in IoT devices.
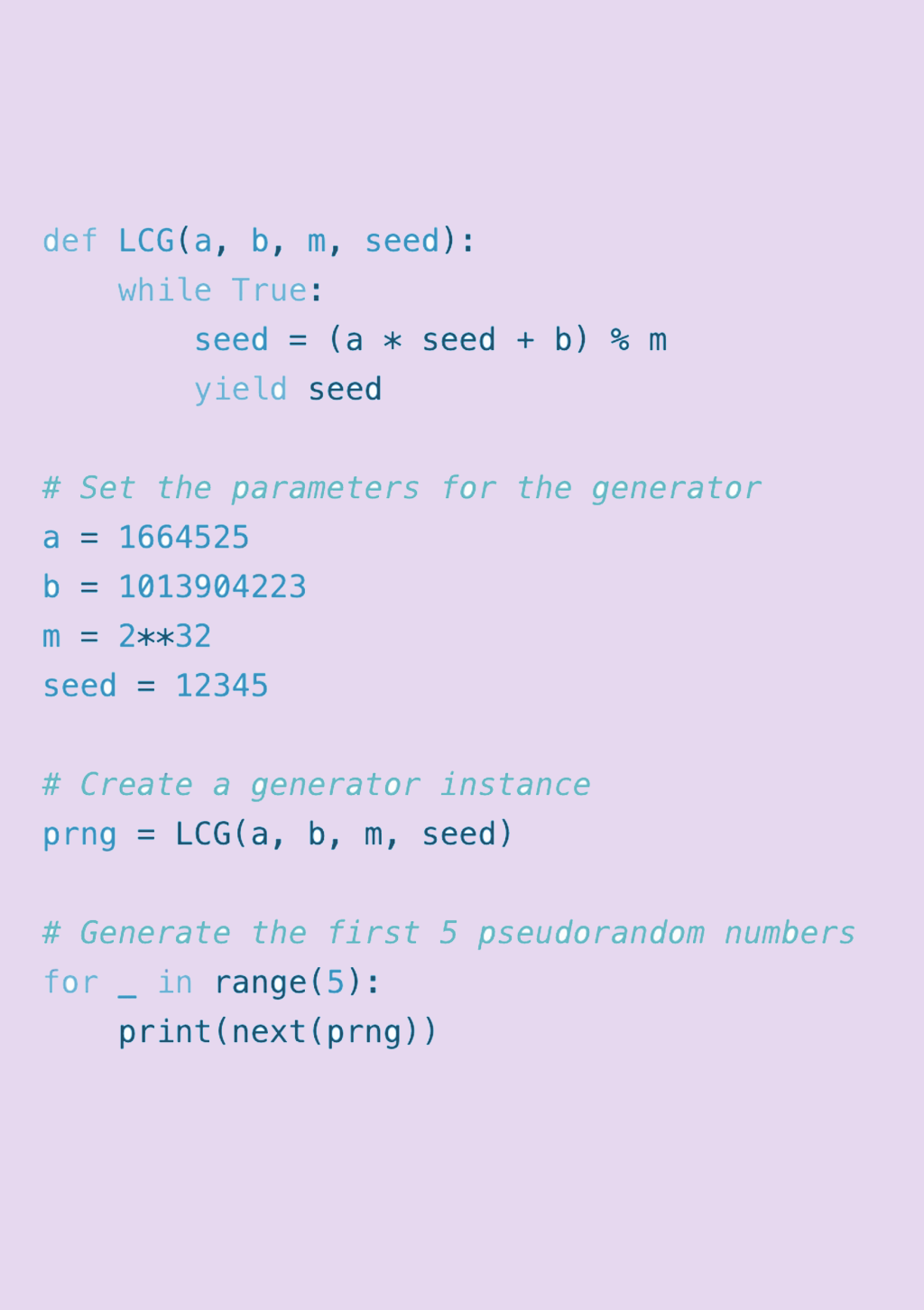
About the image
A piece of code that generates pseudo random numbers.
Illustration by Matt Ballantine, 2026