Questions for you:
- Where do you rely on randomness without realising it? Consider the passwords you create, the security systems you trust, the decisions you make based on numbers you don’t verify yourself.
- How much of your sense of security is based on genuinely impenetrable systems versus simply very large numbers that make attacks impractical? When does “extremely unlikely” become “safe enough”?
- When you create passwords or PINs, do you introduce predictable patterns? Try generating one now without thinking – did you avoid repeating digits, favour certain numbers, or follow substitution rules you’ve used before?
Organisational applications:
Security infrastructure audit: Where does your organisation rely on cryptographic security, and how confident are you that those keys were generated with genuine randomness rather than pseudo-random algorithms that might contain predictable patterns? How can you assess that?
Password policy effectiveness: Do your password policies actually improve security, or do they push employees toward predictable patterns? Requirements like “must include a number and symbol” often result in passwords like “Password1!” rather than genuine randomness.
Legacy system vulnerabilities: Which of your systems were implemented when cryptographic key lengths were considered sufficient but might now be vulnerable? A 128-bit key from 2010 looked unbreakable; quantum computing changes that calculation entirely.
Human factors in security: Where do you allow human choice in security-critical random generation? Every point where someone picks a key rather than generates a key is a potential weakness, regardless of your technical infrastructure.
Further reading
Cryptography fundamentals
- The Code Book by Simon Singh – accessible history of encryption from ancient Caesar cyphers to modern public-key cryptography, explaining why random key generation became essential.
- Cryptography Engineering by Niels Ferguson, Bruce Schneier, and Tadayoshi Kohno – technical but readable explanation of how encryption systems work and why randomness quality matters more than algorithm complexity.
- Bruce Schneier’s blog (www.schneier.com) – ongoing analysis of security failures, many of which trace back to inadequate random number generation rather than algorithmic weaknesses.
Large numbers and probability
- The Drunkard’s Walk by Leonard Mlodinow – explores how humans consistently misjudge probability and randomness, including why we fail to grasp the security implications of truly large numbers.
- How Not to Be Wrong by Jordan Ellenberg – explains why our intuitions about numbers fail us, particularly relevant to understanding why 2^256 possible keys provides meaningful rather than illusory security.
- Scott Aaronson’s blog “Shtetl-Optimized” – quantum computing researcher explaining what large numbers actually mean for security, including which encryption methods remain secure and which become vulnerable.
Random number generation
- Randomness by Deborah Bennett – history of how humans have attempted to generate and use randomness, from ancient divination to modern computing requirements.
- The Art of Computer Programming, Volume 2 (Chapter 3) by Donald Knuth – definitive technical reference on random number generation, explaining tests for randomness quality and why many supposedly random generators produce predictable patterns.
- RFC 4086 “Randomness Requirements for Security” – technical specification explaining what constitutes adequate randomness for cryptographic purposes, freely available online and surprisingly readable for an RFC document.
Interactive exhibit
Increasing the number of digits in a key quite dramatically increases the complexity of cracking it. This little exhibit helps you to visualise that scaling: https://experiments.randomthebook.com/brute_force/
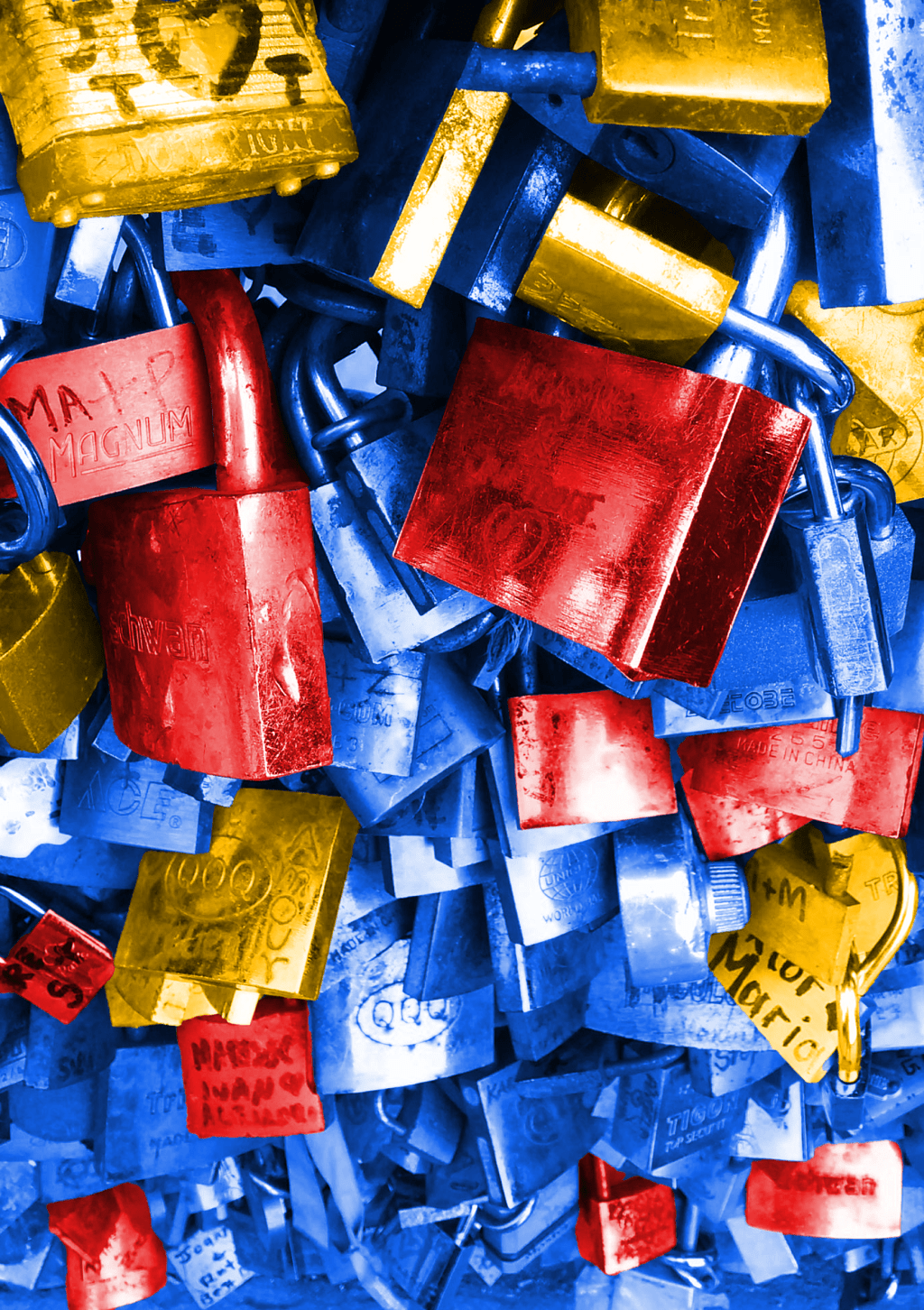
About the image
This photo was taken on a bridge in Paris where people had attached padlocks as a sign of love. Apparently it’s become such a thing in the City that the weight of the padlocks is starting to cause structural problems.
Photo montage and photo by Matt Ballantine, 2026