Questions for you:
- Do I understand the difference between randomness that’s “good enough” and true unpredictability?
- In what contexts do I need genuine randomness versus deterministic processes that appear random?
- What assumptions do I make about the fairness of selection processes that claim to be random?
Organisational applications:
True randomness versus “good enough” randomness:
Distinguish contexts requiring genuine unpredictability (security, fairness, compliance) from situations where pseudo-randomness suffices (simulations, sampling, creative applications). ERNIE used electronic noise from neon tubes because Premium Bonds required verifiable fairness—millions of pounds at stake demanded true randomness, not deterministic algorithms appearing random. Most organisational processes claiming randomness use pseudo-random number generators adequate for their purpose but vulnerable if stakes increase. Audit all processes that claim to use random selection (e.g., hiring lotteries, audit sampling, security token generation) to determine whether the current randomness quality meets the stated requirements. Document which systems need upgrading from deterministic pseudo-randomness to genuine entropy sources when security or fairness implications escalate.
Redundancy and verification in critical random processes:
ERNIE used dual counters for each digit, comparing results and calculating differences to maintain randomness even if one counter failed. This principle—redundant randomness sources with verification—applies beyond 1950s electronics. When random selection entails legal, financial, or reputational consequences, implement multiple independent random number generators and verification protocols. Lottery systems should generate numbers through separate mechanisms, and outputs should be compared to detect failures or manipulation. Security systems should combine hardware entropy sources (e.g., thermal noise, quantum processes) with algorithmic checks that prevent predictable patterns. Track whether redundant random generation reveals failures in primary systems before they produce biased outcomes.
Transparency and auditability of random processes:
Premium Bonds required public trust that the selection was genuinely fair. ERNIE achieved this through physical presence (witnesses could observe the machine), technical documentation (principles were published), and consistent behaviour (the same process every draw). Modern random processes often operate invisibly in software, creating trust problems when fairness matters. Establish transparency protocols for organisational randomness: publish the algorithms used for random selection, enable independent verification of randomness quality, and maintain audit trails that demonstrate that selection processes weren’t manipulated. Compare stakeholder trust in transparent, verifiable random processes with opaque “black box” systems that claim randomness.
Evolution from mechanical to digital randomness:
ERNIE evolved from analogue neon-tube noise (ERNIE 1) through digital systems to current quantum-based technology (ERNIE 5), each generation improving randomness quality whilst maintaining its core purpose. Organisations should audit random processes periodically as technology advances rather than assuming initial implementations remain adequate. What constituted “good enough” randomness in 2000 may prove insufficient in 2025 as computing power enables previously impossible pattern detection. Implement randomness technology refresh cycles, particularly for security-critical applications, as adversary capabilities continually improve. Document whether proactive randomness upgrades prevent vulnerabilities, as opposed to reactive fixes after exploitation.
Further reading
On ERNIE and Premium Bonds:
The ERNIE Archive (Virtual Colossus, online). Comprehensive technical documentation of ERNIE’s design including circuit diagrams, operational principles, and evolution through five generations.
A fairly random thing happened when Matt spoke to his dad about ERNIE: https://randomthebook.com/2024/07/22/dispatches-from-the-frontline-of-randomness-and-serendipity/
The Information: A History, a Theory, a Flood by James Gleick (Pantheon, 2011). Includes discussion of early electronic random number generation and post-war British computing innovations including work at Post Office Research Station where ERNIE was developed.
On random number generation:
Random Number Generation and Monte Carlo Methods by James E. Gentle (Springer, 2nd edition, 2003). Technical examination of random number generation including distinction between true randomness from physical processes versus deterministic pseudo-randomness from algorithms.
The Art of Computer Programming, Volume 2: Seminumerical Algorithms by Donald Knuth (Addison-Wesley, 3rd edition, 1997). Classic computer science text including comprehensive treatment of random number generation, testing randomness quality, and when pseudo-randomness proves inadequate.
Randomness by Deborah J. Bennett (Harvard University Press, 1998). Accessible history of humanity’s understanding of randomness including development of mechanical and electronic random selection devices.
On fairness and verifiable randomness:
The Wisdom of Crowds by James Surowiecki (Doubleday, 2004). Examines conditions under which random selection from populations produces good outcomes, relevant for understanding why random lottery systems can work effectively.
Algorithms to Live By: The Computer Science of Human Decisions by Brian Christian and Tom Griffiths (Henry Holt, 2016). Includes discussion of when random selection outperforms deliberate choice and computational requirements for genuine versus pseudo randomness.
Security Engineering: A Guide to Building Dependable Distributed Systems by Ross Anderson (Wiley, 3rd edition, 2020). Technical examination of randomness requirements for cryptographic security including why deterministic pseudo-randomness proves inadequate for security-critical applications and methods for generating verifiable randomness.
Interactive exhibit
You can play with our ERNIE Simulator here: https://experiments.randomthebook.com/ERNIE/
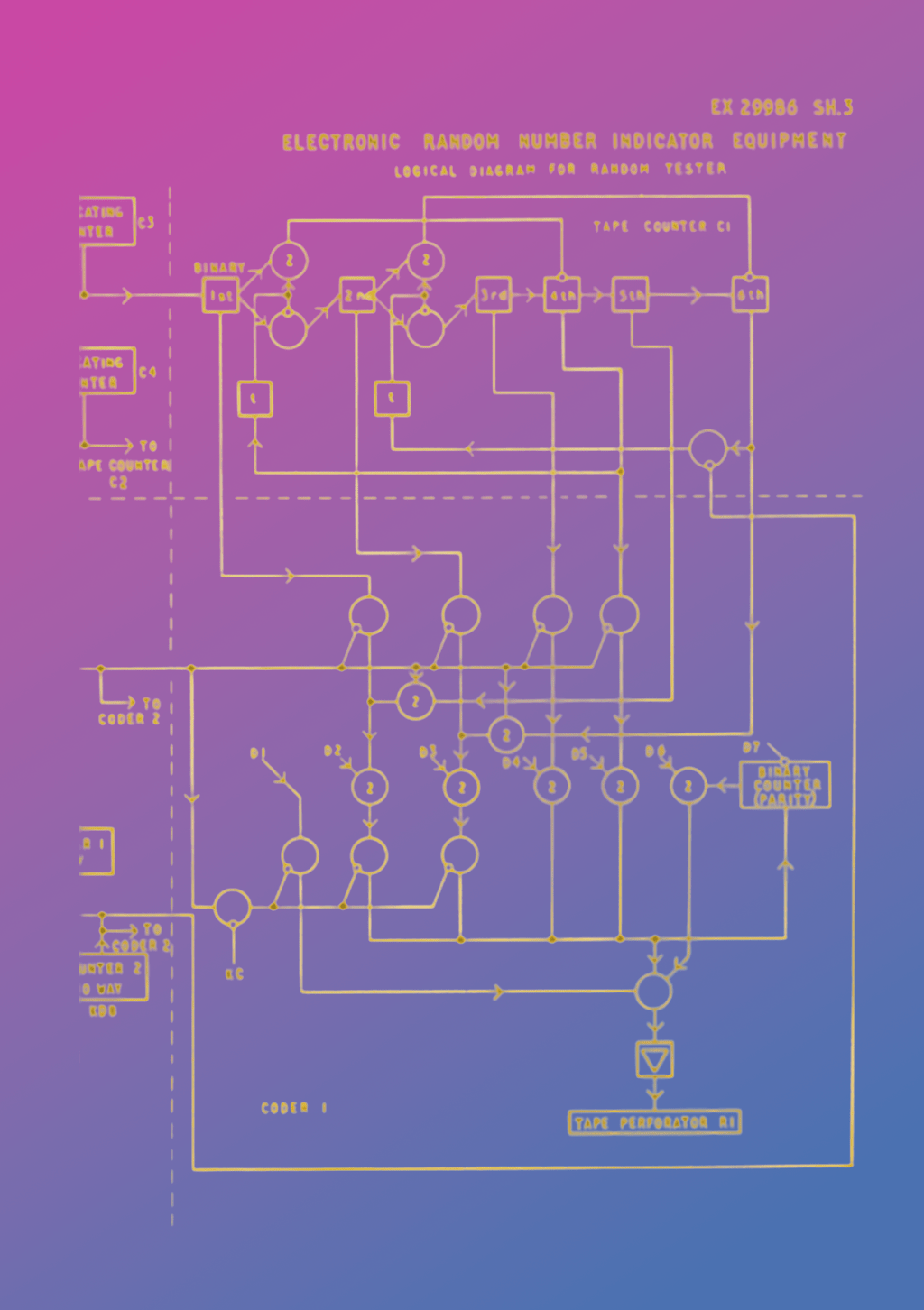
About the image
A small snippet of the orginal circuit diagrams culled from the archive documentation found here:
https://www.digitalarchives.bt.com/Calmview/GetDocument.ashx?db=Catalog&fname=TCB_422%2fTCB_422_20267.pdf
Montage Matt Ballantine 2026